Ephesoft configuration with ADFS over SAML 2.0 with Authentication Type 2
This wiki provides you details related to what all configuration needs to be taken care of when configuring Ephesoft with ADFS over SAML 2.0 with Authentication Type 2. Authentication Type 2 means we are authentication and authorizing using SSO.
Understanding Authentication Type 2
Integrating Ephesoft with Authentication Type 2 means that you are authentication and authorizing with SSO. We will enter the username on the SSO login page which will be forwarded as a SAML Request to the Identity Provider and ephesoft will receive username and associated groups with that user back as a SAML Response. In this article we will not be dealing with Multi Group configuration.
Pre-requisite:
- Active Directory Federation Services Installed
- Active Directory Installed.
- Ephesoft Transact 4.5.0.0 or onwards Installed
Configuration Files Required
- server.xml
- applicationContext.xml
- web.xml
- applicationContext-Security.xml
- dcma-batch.properties
- Ephesoft saml metadata file that needs to be imported at Ephesoft Side.
- ADFS Federation metadata file
- Valid KeyStore (JKS) in which we need to import ADFS certificate.
Checklist components:
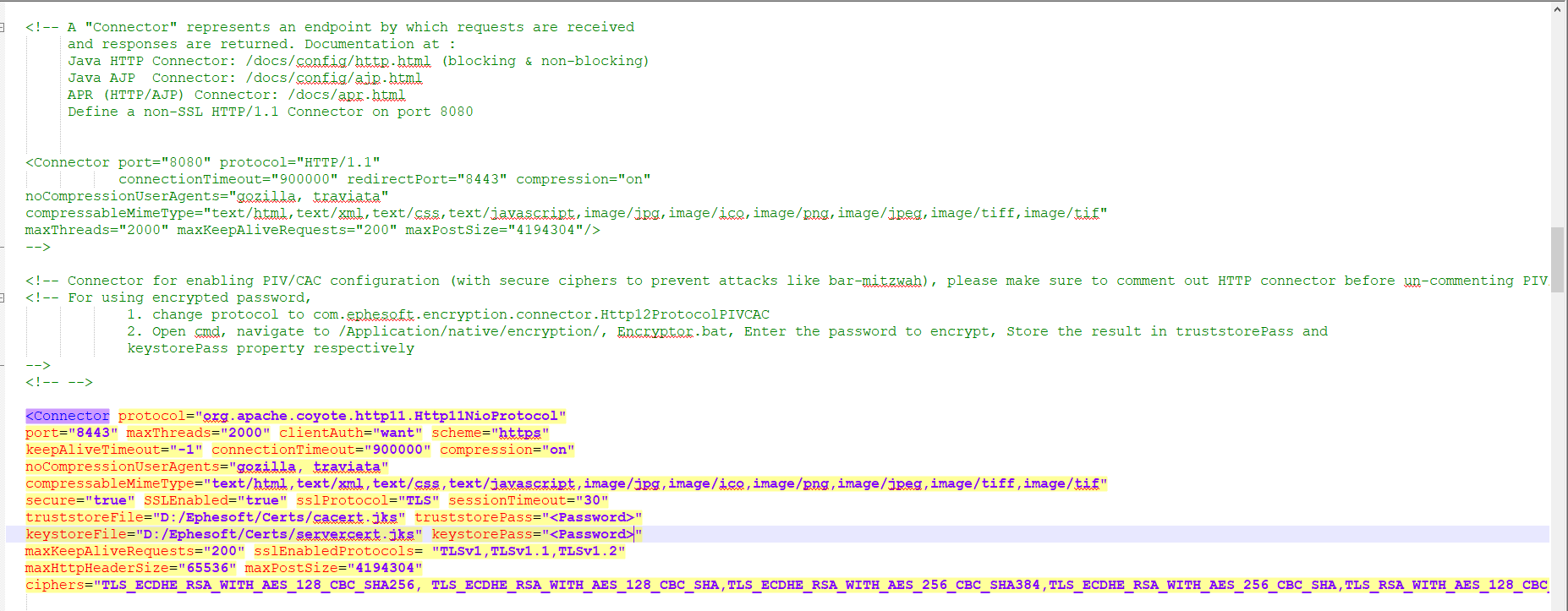
Server.xml
- Configure connection port 8443
- Comment connection port 8080
- Restart the ephesoft service and verify if it works fine over https.
Note:
- You can configure any port over HTTPS. In this article we will be configuring tomcat over SSL over port 8443.
- Refer this article to understand how to configure tomcat over HTTPS.
- Refer this article to understand how to generate truststore and KeyStore
- Download the sample server.xml from here.
- Download truststore and keystore file here. Password for both files is “abhishek”.
Below is the screenshot on how server.xml should look like:
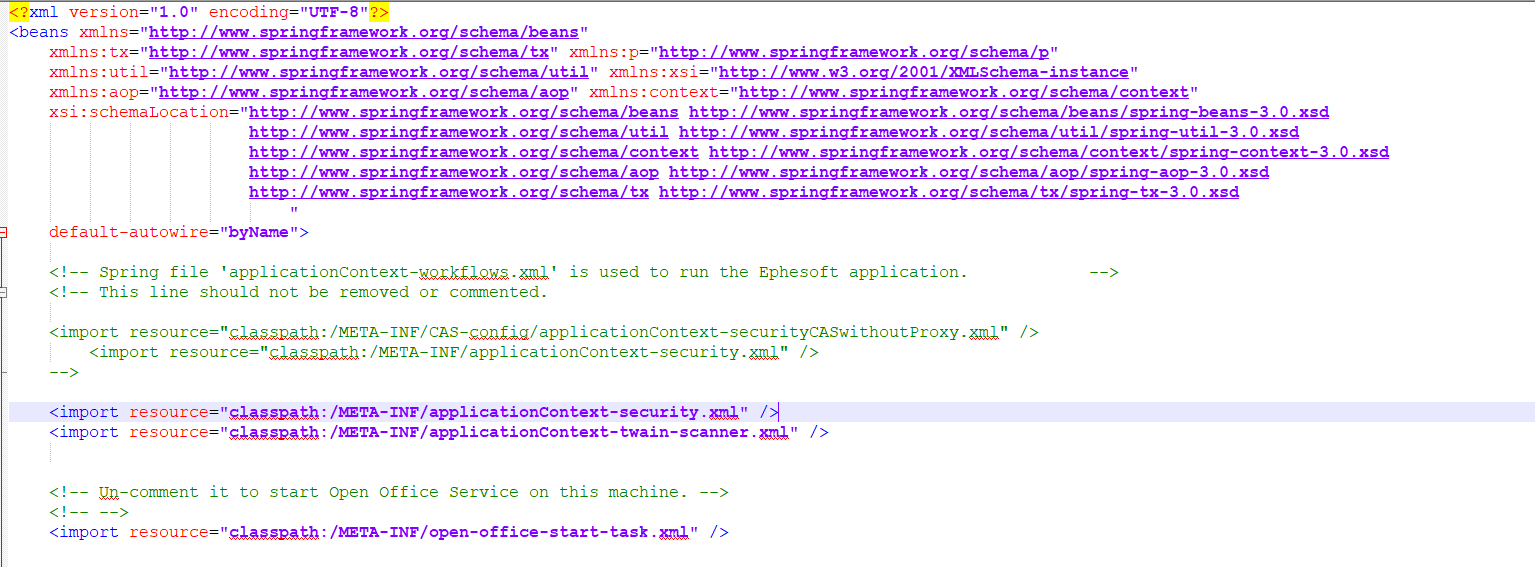
application-context.xml
- Uncomment <import resource=”classpath:/META-INF/applicationContext-security.xml” /> from application-context.xml file.
- Above needs to be done to enable SAML configuration which is configured in applicationContext-security.xml file.
Note:
- Download the sample application-context.xml file from here.
web.xml
- Uncomment the springSecurityFilterChain filter and its filter mapping.
- Comment out the sessionTimeoutFilter and its filter mapping
- Comment out the SessionTimeoutServlet and its Servlet Mapping
- Comment out all security-constraints and
- Comment login-config nodes
- Place authentication filter and its filter mapping below springSecurityFilterChain
- Make change in logout URL to point it to correct port and URL
- Select 2 for authenticationType bean
Note:
- Download the sample web.xml file from here.
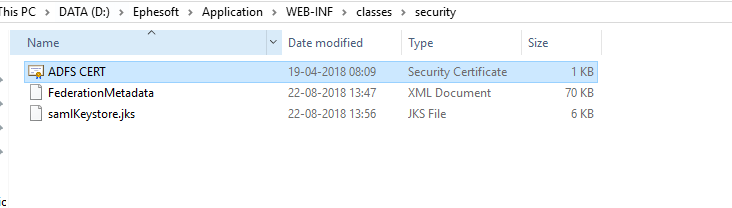
security folder
- Make sure you are placing your sample JKS file in this folder. By default Ephesoft Provides samlKeystore.jks which can be used to configure Ephesoft.
- Make sure the ADFS cert is imported in the above JKS file
- Make sure you have download FederationMetadata file in xml format from your ADFS server and placed the same in security folder.
- Command to import ADFS cert to is keytool.exe -importcert -alias <alias name> -keystore “<Keystore path>” -file “<cert path>”
- Hit https://<<domainname>>/FederationMetadata/2007-06/FederationMetadata.xml and get the ADFS metadata file and save it in security folder.
Note:
- Download the sample security folder from here. Please note that ADFS Metadata file and the cert will not work at your end. This is only for reference purpose
applicationContext-security.xml
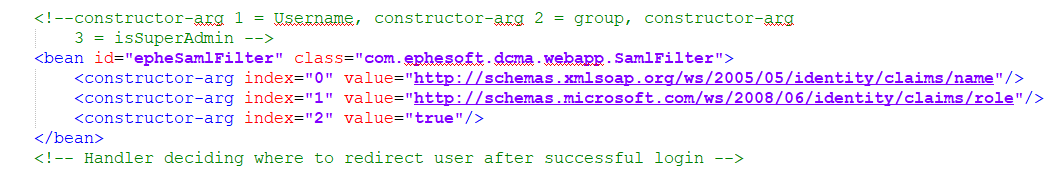
- Change the constructor arguments for epheSamlFilter bean.These constructor-arg values are based on the rule language you define in ADFS Claim Rules. Argument index 0 takes username details and argument 2 takes group details.
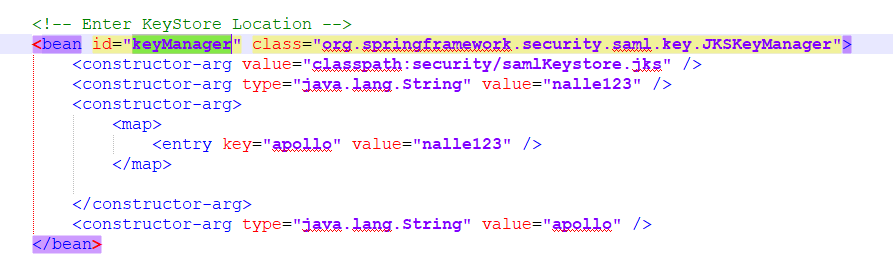
- If you have created you own keystore then make sure you are providing correct name and path of the keystore file and keystore password.
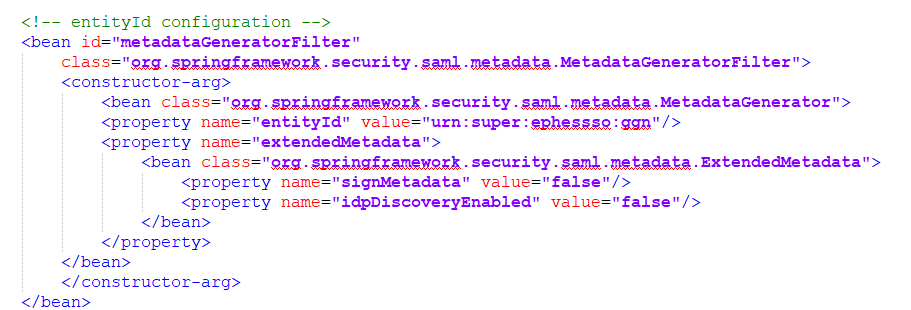
- Make sure entityId entered here is correct and is same as what you will be defining in ADFS. EntityId is defined in the value attribute of “entityId” property name
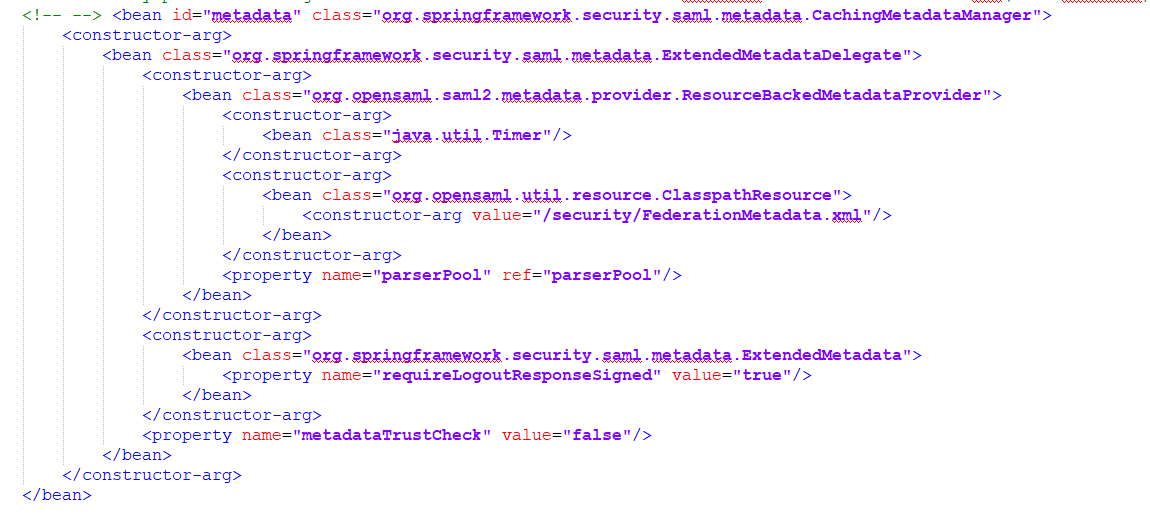
- Make changes in metaDataFilter Bean and metaData filter. Make sure to use correct metadata bean as defined in this file. Make sure you provide correct name for the FederatinMetadata.xml file
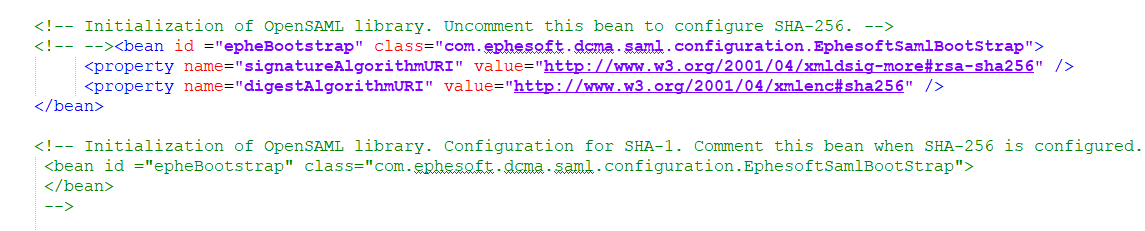
- Based on the Secure hash algorithm make sure you comment / uncomment SHA-1 or SHA-256 which is controlled by bean as seen in below screenshot.
Note:
- Download the sample applicationContext-Security.xml from here.
Configuration Settings at Active Directory Federation Services
- Follow this wiki article on understanding how configuration needs to be done at ADFS side.
Order of configuring SSO
In this section you will understand the order in which each of the above mentioned files needs to be configured.
- Start with generating JKS files for to configure tomcat over SSL if you do not have truststore and keystore prior.
- Configure tomcat over https and also make changes in dcma-batch.properties file and workflow.properties file for batch.base_http_url and wb.hostURL properties respectively.
- Start configuration changes in applicationContext.xml, web.xml file.
- Create JKS file if you want provided in the security folder.
- Download the ADFS certificate and FederationMetaDataFile from ADFS and place it in security folder.
- Make changes in applicationContext-Security file, remember to take care of the changes as mentioned above.
- Download the ephesoft metadata file and import the file to create relying party trust on ADFS.
- Make sure all the properties are correct for relying party created and now create claim rules.
- Restart the ephesoft service.
Final Output Screens:
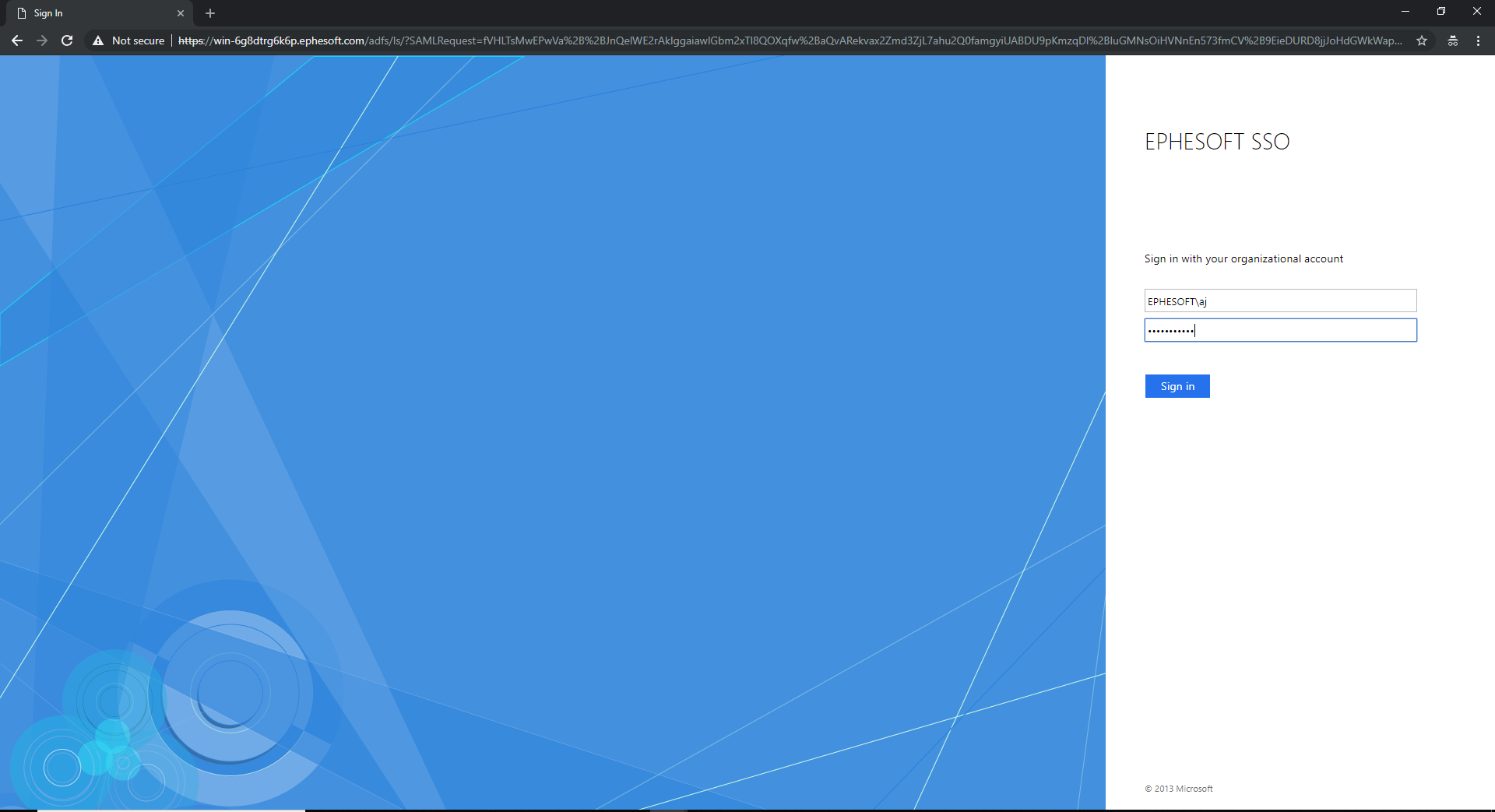
- Hit Ephesoft URL on the browser and you should be redirected to ADFS URL and screen.
- Enter the username and password on the SSO page.
3. If everything is configured correctly then you will now be redirected to Ephesoft Home Page and Now you can select the option / screen that you want look into.